با تخفیف
-
 مانتو چهار خانه پشمی شنل دار آستین بافت
مانتو چهار خانه پشمی شنل دار آستین بافت
تومان790,000قیمت اصلی تومان790,000 بود.تومان590,000قیمت فعلی تومان590,000 است. -
 مانتو ریما آستین بافت قواره
مانتو ریما آستین بافت قواره
تومان890,000قیمت اصلی تومان890,000 بود.تومان690,000قیمت فعلی تومان690,000 است. -
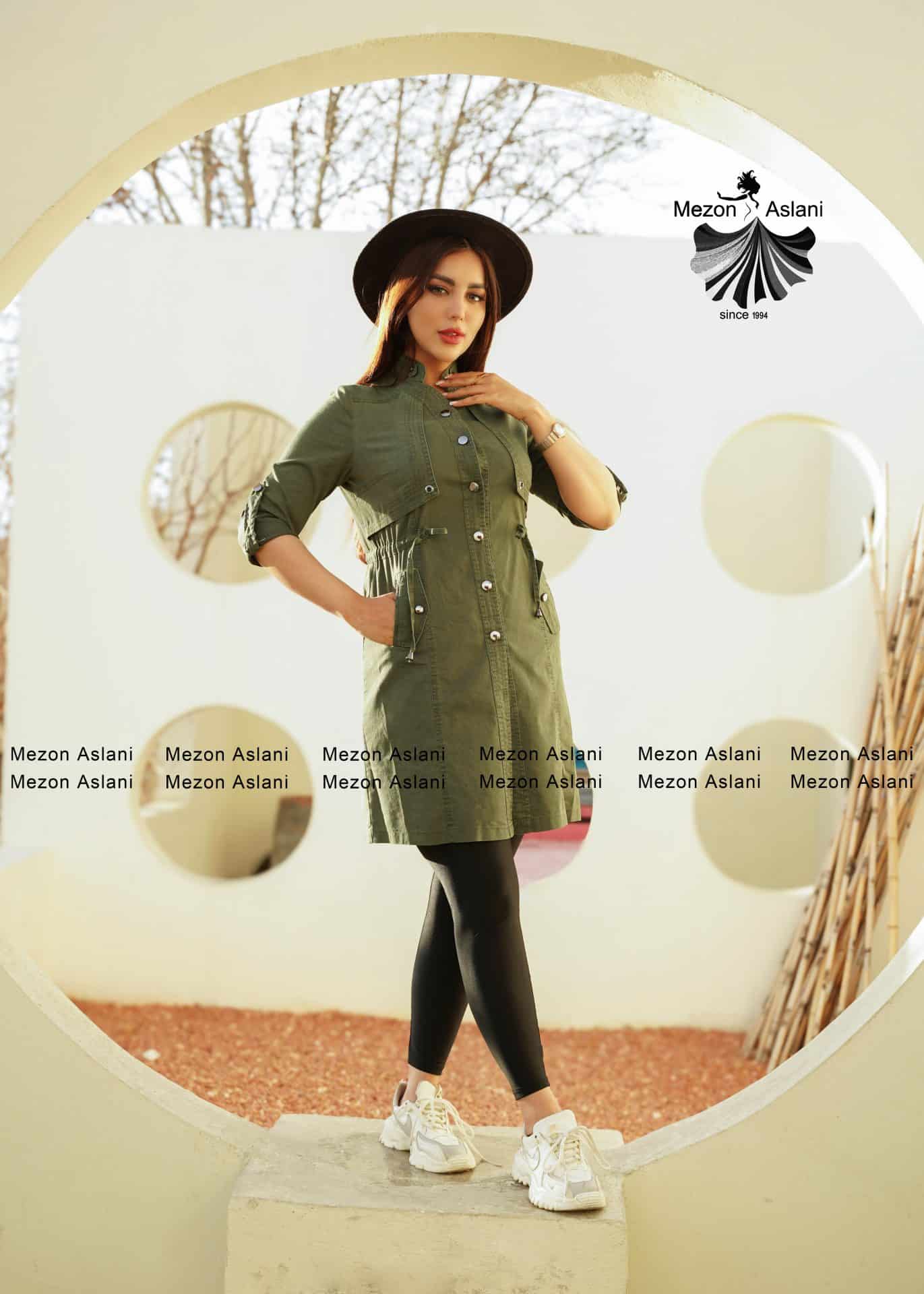
 بارانی سوپر سانتانا
بارانی سوپر سانتانا
تومان1,300,000قیمت اصلی تومان1,300,000 بود.تومان990,000قیمت فعلی تومان990,000 است. -
 کاپشن سیلیکونی
کاپشن سیلیکونی
تومان960,000قیمت اصلی تومان960,000 بود.تومان790,000قیمت فعلی تومان790,000 است.
Whether your goal is to keep your finances, your identity or perhaps your privateness secure, you need coverage. Anti virus software is your very best defense against malicious code, including malware, worms, Trojan horses, spy ware and other trojans. But how exactly does antivirus computer software identify potential viruses?
The first antivirus programs simply looked for the digital personal unsecured that would distinctively identify a virus record. For example , a scanner may search memory and the start sector in disk for the purpose of code thoughts that are typically found only in viruses (not in benign programs). This software then even comes close these to an existing list of malware to determine unique dangerous.
Classic antivirus software program still uses these signature-based strategies to protect users from well-known threats. Which means that when a new file is usually downloaded, the technology scans its database of signatures for a match. If a match is located, the program flags the file for the reason that malevolent.
This is not a foolproof method since many malware are created simply by hackers just for nefarious usages. For example , a program that was at first designed to display how it could spread from a computer to a different was later on used to encounter companies that http://webroot-reviews.com/what-are-the-potential-profits-of-data-room-software-for-private-equity-firms/ give virus encoding software. The result was a computer virus called Creeper, which packed itself into memory just before anti-virus software program started running and prevented this from performing properly.
Several antivirus courses are able to identify these hotter threats through the use of heuristic detection techniques. Using this method runs files in a online environment and records their very own behavior. After that it looks for patterns of activity that are usually associated with malignant activity, such as adjusting or deleting files, monitoring keystrokes or changing the settings of other courses. If a shady activity is usually identified, the antivirus definitely will quarantine or isolate the file and/or program, and it will manage an additional examination on them in a “sandbox” to determine whether they may be safely executed in the actual.












دیدگاهتان را بنویسید